11 changed files with 396 additions and 3 deletions
+ 11
- 3
models/oauth2.go
View File
| ProfileURL: oauth2.GetDefaultProfileURL("gitea"), | ProfileURL: oauth2.GetDefaultProfileURL("gitea"), | ||||
| }, | }, | ||||
| }, | }, | ||||
| "nextcloud": {Name: "nextcloud", DisplayName: "Nextcloud", Image: "/img/auth/nextcloud.png", | |||||
| CustomURLMapping: &oauth2.CustomURLMapping{ | |||||
| TokenURL: oauth2.GetDefaultTokenURL("nextcloud"), | |||||
| AuthURL: oauth2.GetDefaultAuthURL("nextcloud"), | |||||
| ProfileURL: oauth2.GetDefaultProfileURL("nextcloud"), | |||||
| }, | |||||
| }, | |||||
| } | } | ||||
| // OAuth2DefaultCustomURLMappings contains the map of default URL's for OAuth2 providers that are allowed to have custom urls | // OAuth2DefaultCustomURLMappings contains the map of default URL's for OAuth2 providers that are allowed to have custom urls | ||||
| // key is used to map the OAuth2Provider | // key is used to map the OAuth2Provider | ||||
| // value is the mapping as defined for the OAuth2Provider | // value is the mapping as defined for the OAuth2Provider | ||||
| var OAuth2DefaultCustomURLMappings = map[string]*oauth2.CustomURLMapping{ | var OAuth2DefaultCustomURLMappings = map[string]*oauth2.CustomURLMapping{ | ||||
| "github": OAuth2Providers["github"].CustomURLMapping, | |||||
| "gitlab": OAuth2Providers["gitlab"].CustomURLMapping, | |||||
| "gitea": OAuth2Providers["gitea"].CustomURLMapping, | |||||
| "github": OAuth2Providers["github"].CustomURLMapping, | |||||
| "gitlab": OAuth2Providers["gitlab"].CustomURLMapping, | |||||
| "gitea": OAuth2Providers["gitea"].CustomURLMapping, | |||||
| "nextcloud": OAuth2Providers["nextcloud"].CustomURLMapping, | |||||
| } | } | ||||
| // GetActiveOAuth2ProviderLoginSources returns all actived LoginOAuth2 sources | // GetActiveOAuth2ProviderLoginSources returns all actived LoginOAuth2 sources |
+ 23
- 0
modules/auth/oauth2/oauth2.go
View File
| "github.com/markbates/goth/providers/github" | "github.com/markbates/goth/providers/github" | ||||
| "github.com/markbates/goth/providers/gitlab" | "github.com/markbates/goth/providers/gitlab" | ||||
| "github.com/markbates/goth/providers/google" | "github.com/markbates/goth/providers/google" | ||||
| "github.com/markbates/goth/providers/nextcloud" | |||||
| "github.com/markbates/goth/providers/openidConnect" | "github.com/markbates/goth/providers/openidConnect" | ||||
| "github.com/markbates/goth/providers/twitter" | "github.com/markbates/goth/providers/twitter" | ||||
| "github.com/satori/go.uuid" | "github.com/satori/go.uuid" | ||||
| } | } | ||||
| } | } | ||||
| provider = gitea.NewCustomisedURL(clientID, clientSecret, callbackURL, authURL, tokenURL, profileURL) | provider = gitea.NewCustomisedURL(clientID, clientSecret, callbackURL, authURL, tokenURL, profileURL) | ||||
| case "nextcloud": | |||||
| authURL := nextcloud.AuthURL | |||||
| tokenURL := nextcloud.TokenURL | |||||
| profileURL := nextcloud.ProfileURL | |||||
| if customURLMapping != nil { | |||||
| if len(customURLMapping.AuthURL) > 0 { | |||||
| authURL = customURLMapping.AuthURL | |||||
| } | |||||
| if len(customURLMapping.TokenURL) > 0 { | |||||
| tokenURL = customURLMapping.TokenURL | |||||
| } | |||||
| if len(customURLMapping.ProfileURL) > 0 { | |||||
| profileURL = customURLMapping.ProfileURL | |||||
| } | |||||
| } | |||||
| provider = nextcloud.NewCustomisedURL(clientID, clientSecret, callbackURL, authURL, tokenURL, profileURL) | |||||
| } | } | ||||
| // always set the name if provider is created so we can support multiple setups of 1 provider | // always set the name if provider is created so we can support multiple setups of 1 provider | ||||
| return gitlab.TokenURL | return gitlab.TokenURL | ||||
| case "gitea": | case "gitea": | ||||
| return gitea.TokenURL | return gitea.TokenURL | ||||
| case "nextcloud": | |||||
| return nextcloud.TokenURL | |||||
| } | } | ||||
| return "" | return "" | ||||
| } | } | ||||
| return gitlab.AuthURL | return gitlab.AuthURL | ||||
| case "gitea": | case "gitea": | ||||
| return gitea.AuthURL | return gitea.AuthURL | ||||
| case "nextcloud": | |||||
| return nextcloud.AuthURL | |||||
| } | } | ||||
| return "" | return "" | ||||
| } | } | ||||
| return gitlab.ProfileURL | return gitlab.ProfileURL | ||||
| case "gitea": | case "gitea": | ||||
| return gitea.ProfileURL | return gitea.ProfileURL | ||||
| case "nextcloud": | |||||
| return nextcloud.ProfileURL | |||||
| } | } | ||||
| return "" | return "" | ||||
| } | } |
+ 1
- 0
options/locale/locale_en-US.ini
View File
| auths.tips.oauth2.general.tip = When registering a new OAuth2 authentication, the callback/redirect URL should be: <host>/user/oauth2/<Authentication Name>/callback | auths.tips.oauth2.general.tip = When registering a new OAuth2 authentication, the callback/redirect URL should be: <host>/user/oauth2/<Authentication Name>/callback | ||||
| auths.tip.oauth2_provider = OAuth2 Provider | auths.tip.oauth2_provider = OAuth2 Provider | ||||
| auths.tip.bitbucket = Register a new OAuth consumer on https://bitbucket.org/account/user/<your username>/oauth-consumers/new and add the permission 'Account' - 'Read' | auths.tip.bitbucket = Register a new OAuth consumer on https://bitbucket.org/account/user/<your username>/oauth-consumers/new and add the permission 'Account' - 'Read' | ||||
| auths.tip.nextcloud = Register a new OAuth consumer on your instance using the following menu "Settings -> Security -> OAuth 2.0 client" | |||||
| auths.tip.dropbox = Create a new application at https://www.dropbox.com/developers/apps | auths.tip.dropbox = Create a new application at https://www.dropbox.com/developers/apps | ||||
| auths.tip.facebook = Register a new application at https://developers.facebook.com/apps and add the product "Facebook Login" | auths.tip.facebook = Register a new application at https://developers.facebook.com/apps and add the product "Facebook Login" | ||||
| auths.tip.github = Register a new OAuth application on https://github.com/settings/applications/new | auths.tip.github = Register a new OAuth application on https://github.com/settings/applications/new |
BIN
public/img/auth/nextcloud.png
View File

+ 2
- 0
templates/admin/auth/new.tmpl
View File
| <span>{{.i18n.Tr "admin.auths.tip.discord"}}</span> | <span>{{.i18n.Tr "admin.auths.tip.discord"}}</span> | ||||
| <li>Gitea</li> | <li>Gitea</li> | ||||
| <span>{{.i18n.Tr "admin.auths.tip.gitea"}}</span> | <span>{{.i18n.Tr "admin.auths.tip.gitea"}}</span> | ||||
| <li>Nextcloud</li> | |||||
| <span>{{.i18n.Tr "admin.auths.tip.nextcloud"}}</span> | |||||
| </div> | </div> | ||||
| </div> | </div> | ||||
| </div> | </div> |
+ 85
- 0
vendor/github.com/markbates/goth/providers/nextcloud/README.md
View File
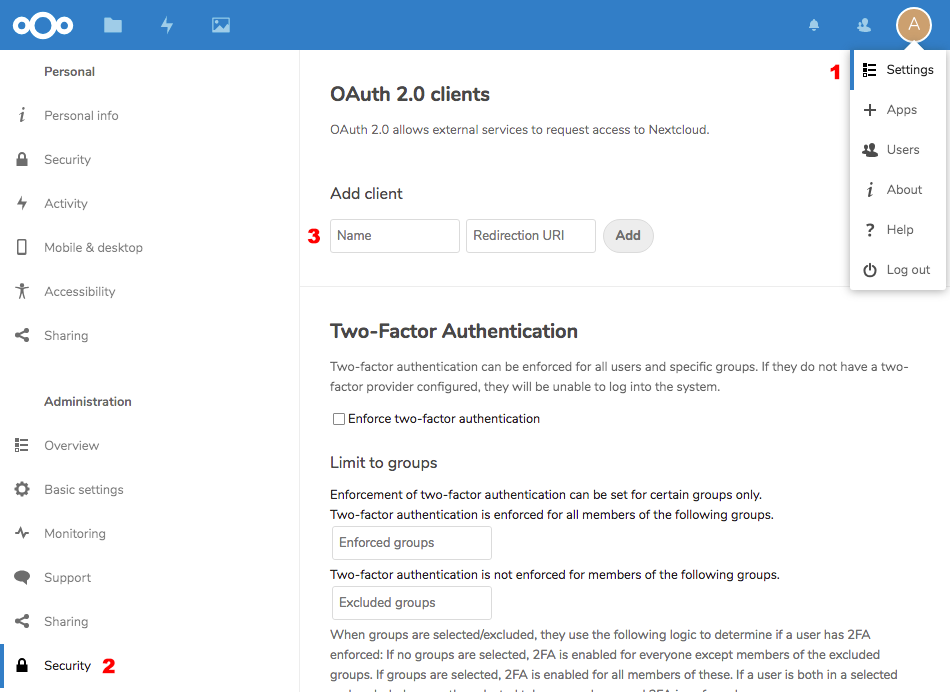
| # Nextcloud OAuth2 | |||||
| For this backend, you need to have an OAuth2 enabled Nextcloud Instance, e.g. | |||||
| on your own private server. | |||||
| ## Setting up Nextcloud Test Environment | |||||
| To test, you only need a working Docker image of Nextcloud running on a public | |||||
| URL, e.g. through [traefik](https://traefik.io/) | |||||
| ```docker-compose.yml | |||||
| version: '2' | |||||
| networks: | |||||
| traefik-web: | |||||
| external: true | |||||
| services: | |||||
| app: | |||||
| image: nextcloud | |||||
| restart: always | |||||
| networks: | |||||
| - traefik-web | |||||
| labels: | |||||
| - traefik.enable=true | |||||
| - traefik.frontend.rule=Host:${NEXTCLOUD_DNS} | |||||
| - traefik.docker.network=traefik-web | |||||
| environment: | |||||
| SQLITE_DATABASE: "database.sqlite3" | |||||
| NEXTCLOUD_ADMIN_USER: admin | |||||
| NEXTCLOUD_ADMIN_PASSWORD: admin | |||||
| NEXTCLOUD_TRUSTED_DOMAINS: ${NEXTCLOUD_DNS} | |||||
| ``` | |||||
| and start it up via | |||||
| ``` | |||||
| NEXTCLOUD_DNS=goth.my.server.name docker-compose up -d | |||||
| ``` | |||||
| afterwards, you will have a running Nextcloud instance with credentials | |||||
| ``` | |||||
| admin / admin | |||||
| ``` | |||||
| Then add a new OAuth 2.0 Client by going to | |||||
| ``` | |||||
| Settings -> Security -> OAuth 2.0 client | |||||
| ``` | |||||
|  | |||||
| and add a new client with the name `goth` and redirection uri `http://localhost:3000/auth/nextcloud/callback`. The imporant part here the | |||||
| two cryptic entries `Client Identifier` and `Secret`, which needs to be | |||||
| used in your application. | |||||
| ## Running Login Example | |||||
| If you want to run the default example in `<goth>/examples`, you have to | |||||
| retrieve the keys described in the previous section and run the example | |||||
| as follows: | |||||
| ``` | |||||
| NEXTCLOUD_URL=https://goth.my.server.name \ | |||||
| NEXTCLOUD_KEY=<your-key> \ | |||||
| NEXTCLOUD_SECRET=<your-secret> \ | |||||
| SESSION_SECRET=1 \ | |||||
| ./examples | |||||
| ``` | |||||
| Afterwards, you should be able to login via Nextcloud in the examples app. | |||||
| ## Running the Provider Test | |||||
| The test has the same arguments as the login example test, but starts the test itself | |||||
| ``` | |||||
| NEXTCLOUD_URL=https://goth.my.server.name \ | |||||
| NEXTCLOUD_KEY=<your-key> \ | |||||
| NEXTCLOUD_SECRET=<your-secret> \ | |||||
| SESSION_SECRET=1 \ | |||||
| go test -v | |||||
| ``` |
+ 208
- 0
vendor/github.com/markbates/goth/providers/nextcloud/nextcloud.go
View File
| // Package nextcloud implements the OAuth2 protocol for authenticating users through nextcloud. | |||||
| // This package can be used as a reference implementation of an OAuth2 provider for Goth. | |||||
| package nextcloud | |||||
| import ( | |||||
| "bytes" | |||||
| "encoding/json" | |||||
| "io" | |||||
| "io/ioutil" | |||||
| "net/http" | |||||
| "fmt" | |||||
| "github.com/markbates/goth" | |||||
| "golang.org/x/oauth2" | |||||
| ) | |||||
| // These vars define the Authentication, Token, and Profile URLS for Nextcloud. | |||||
| // You have to set these values to something useful, because nextcloud is always | |||||
| // hosted somewhere. | |||||
| // | |||||
| var ( | |||||
| AuthURL = "https://<own-server>/apps/oauth2/authorize" | |||||
| TokenURL = "https://<own-server>/apps/oauth2/api/v1/token" | |||||
| ProfileURL = "https://<own-server>/ocs/v2.php/cloud/user?format=json" | |||||
| ) | |||||
| // Provider is the implementation of `goth.Provider` for accessing Nextcloud. | |||||
| type Provider struct { | |||||
| ClientKey string | |||||
| Secret string | |||||
| CallbackURL string | |||||
| HTTPClient *http.Client | |||||
| config *oauth2.Config | |||||
| providerName string | |||||
| authURL string | |||||
| tokenURL string | |||||
| profileURL string | |||||
| } | |||||
| // New is only here to fulfill the interface requirements and does not work properly without | |||||
| // setting your own Nextcloud connect parameters, more precisely AuthURL, TokenURL and ProfileURL. | |||||
| // Please use NewCustomisedDNS with the beginning of your URL or NewCustomiseURL. | |||||
| func New(clientKey, secret, callbackURL string, scopes ...string) *Provider { | |||||
| return NewCustomisedURL(clientKey, secret, callbackURL, AuthURL, TokenURL, ProfileURL, scopes...) | |||||
| } | |||||
| // NewCustomisedURL create a working connection to your Nextcloud server given by the values | |||||
| // authURL, tokenURL and profileURL. | |||||
| // If you want to use a simpler method, please have a look at NewCustomisedDNS, which gets only | |||||
| // on parameter instead of three. | |||||
| func NewCustomisedURL(clientKey, secret, callbackURL, authURL, tokenURL, profileURL string, scopes ...string) *Provider { | |||||
| p := &Provider{ | |||||
| ClientKey: clientKey, | |||||
| Secret: secret, | |||||
| CallbackURL: callbackURL, | |||||
| providerName: "nextcloud", | |||||
| profileURL: profileURL, | |||||
| } | |||||
| p.config = newConfig(p, authURL, tokenURL, scopes) | |||||
| return p | |||||
| } | |||||
| // NewCustomisedDNS is the simplest method to create a provider based only on your key/secret | |||||
| // and the beginning of the URL to your server, e.g. https://my.server.name/ | |||||
| func NewCustomisedDNS(clientKey, secret, callbackURL, nextcloudURL string, scopes ...string) *Provider { | |||||
| return NewCustomisedURL( | |||||
| clientKey, | |||||
| secret, | |||||
| callbackURL, | |||||
| nextcloudURL+"/apps/oauth2/authorize", | |||||
| nextcloudURL+"/apps/oauth2/api/v1/token", | |||||
| nextcloudURL+"/ocs/v2.php/cloud/user?format=json", | |||||
| scopes..., | |||||
| ) | |||||
| } | |||||
| // Name is the name used to retrieve this provider later. | |||||
| func (p *Provider) Name() string { | |||||
| return p.providerName | |||||
| } | |||||
| // SetName is to update the name of the provider (needed in case of multiple providers of 1 type) | |||||
| func (p *Provider) SetName(name string) { | |||||
| p.providerName = name | |||||
| } | |||||
| func (p *Provider) Client() *http.Client { | |||||
| return goth.HTTPClientWithFallBack(p.HTTPClient) | |||||
| } | |||||
| // Debug is a no-op for the nextcloud package. | |||||
| func (p *Provider) Debug(debug bool) {} | |||||
| // BeginAuth asks Nextcloud for an authentication end-point. | |||||
| func (p *Provider) BeginAuth(state string) (goth.Session, error) { | |||||
| return &Session{ | |||||
| AuthURL: p.config.AuthCodeURL(state), | |||||
| }, nil | |||||
| } | |||||
| // FetchUser will go to Nextcloud and access basic information about the user. | |||||
| func (p *Provider) FetchUser(session goth.Session) (goth.User, error) { | |||||
| sess := session.(*Session) | |||||
| user := goth.User{ | |||||
| AccessToken: sess.AccessToken, | |||||
| Provider: p.Name(), | |||||
| RefreshToken: sess.RefreshToken, | |||||
| ExpiresAt: sess.ExpiresAt, | |||||
| } | |||||
| if user.AccessToken == "" { | |||||
| // data is not yet retrieved since accessToken is still empty | |||||
| return user, fmt.Errorf("%s cannot get user information without accessToken", p.providerName) | |||||
| } | |||||
| req, err := http.NewRequest("GET", p.profileURL, nil) | |||||
| if err != nil { | |||||
| return user, err | |||||
| } | |||||
| req.Header.Set("Authorization", "Bearer "+sess.AccessToken) | |||||
| response, err := p.Client().Do(req) | |||||
| if err != nil { | |||||
| if response != nil { | |||||
| response.Body.Close() | |||||
| } | |||||
| return user, err | |||||
| } | |||||
| defer response.Body.Close() | |||||
| if response.StatusCode != http.StatusOK { | |||||
| return user, fmt.Errorf("%s responded with a %d trying to fetch user information", p.providerName, response.StatusCode) | |||||
| } | |||||
| bits, err := ioutil.ReadAll(response.Body) | |||||
| if err != nil { | |||||
| return user, err | |||||
| } | |||||
| err = json.NewDecoder(bytes.NewReader(bits)).Decode(&user.RawData) | |||||
| if err != nil { | |||||
| return user, err | |||||
| } | |||||
| err = userFromReader(bytes.NewReader(bits), &user) | |||||
| return user, err | |||||
| } | |||||
| func newConfig(provider *Provider, authURL, tokenURL string, scopes []string) *oauth2.Config { | |||||
| c := &oauth2.Config{ | |||||
| ClientID: provider.ClientKey, | |||||
| ClientSecret: provider.Secret, | |||||
| RedirectURL: provider.CallbackURL, | |||||
| Endpoint: oauth2.Endpoint{ | |||||
| AuthURL: authURL, | |||||
| TokenURL: tokenURL, | |||||
| }, | |||||
| Scopes: []string{}, | |||||
| } | |||||
| if len(scopes) > 0 { | |||||
| for _, scope := range scopes { | |||||
| c.Scopes = append(c.Scopes, scope) | |||||
| } | |||||
| } | |||||
| return c | |||||
| } | |||||
| func userFromReader(r io.Reader, user *goth.User) error { | |||||
| u := struct { | |||||
| Ocs struct { | |||||
| Data struct { | |||||
| EMail string `json:"email"` | |||||
| DisplayName string `json:"display-name"` | |||||
| ID string `json:"id"` | |||||
| Address string `json:"address"` | |||||
| } | |||||
| } `json:"ocs"` | |||||
| }{} | |||||
| err := json.NewDecoder(r).Decode(&u) | |||||
| if err != nil { | |||||
| return err | |||||
| } | |||||
| user.Email = u.Ocs.Data.EMail | |||||
| user.Name = u.Ocs.Data.DisplayName | |||||
| user.UserID = u.Ocs.Data.ID | |||||
| user.Location = u.Ocs.Data.Address | |||||
| return nil | |||||
| } | |||||
| //RefreshTokenAvailable refresh token is provided by auth provider or not | |||||
| func (p *Provider) RefreshTokenAvailable() bool { | |||||
| return true | |||||
| } | |||||
| //RefreshToken get new access token based on the refresh token | |||||
| func (p *Provider) RefreshToken(refreshToken string) (*oauth2.Token, error) { | |||||
| token := &oauth2.Token{RefreshToken: refreshToken} | |||||
| ts := p.config.TokenSource(goth.ContextForClient(p.Client()), token) | |||||
| newToken, err := ts.Token() | |||||
| if err != nil { | |||||
| return nil, err | |||||
| } | |||||
| return newToken, err | |||||
| } |
BIN
vendor/github.com/markbates/goth/providers/nextcloud/nextcloud_setup.png
View File
+ 63
- 0
vendor/github.com/markbates/goth/providers/nextcloud/session.go
View File
| package nextcloud | |||||
| import ( | |||||
| "encoding/json" | |||||
| "errors" | |||||
| "strings" | |||||
| "time" | |||||
| "github.com/markbates/goth" | |||||
| ) | |||||
| // Session stores data during the auth process with Nextcloud. | |||||
| type Session struct { | |||||
| AuthURL string | |||||
| AccessToken string | |||||
| RefreshToken string | |||||
| ExpiresAt time.Time | |||||
| } | |||||
| var _ goth.Session = &Session{} | |||||
| // GetAuthURL will return the URL set by calling the `BeginAuth` function on the Nextcloud provider. | |||||
| func (s Session) GetAuthURL() (string, error) { | |||||
| if s.AuthURL == "" { | |||||
| return "", errors.New(goth.NoAuthUrlErrorMessage) | |||||
| } | |||||
| return s.AuthURL, nil | |||||
| } | |||||
| // Authorize the session with Nextcloud and return the access token to be stored for future use. | |||||
| func (s *Session) Authorize(provider goth.Provider, params goth.Params) (string, error) { | |||||
| p := provider.(*Provider) | |||||
| token, err := p.config.Exchange(goth.ContextForClient(p.Client()), params.Get("code")) | |||||
| if err != nil { | |||||
| return "", err | |||||
| } | |||||
| if !token.Valid() { | |||||
| return "", errors.New("Invalid token received from provider") | |||||
| } | |||||
| s.AccessToken = token.AccessToken | |||||
| s.RefreshToken = token.RefreshToken | |||||
| s.ExpiresAt = token.Expiry | |||||
| return token.AccessToken, err | |||||
| } | |||||
| // Marshal the session into a string | |||||
| func (s Session) Marshal() string { | |||||
| b, _ := json.Marshal(s) | |||||
| return string(b) | |||||
| } | |||||
| func (s Session) String() string { | |||||
| return s.Marshal() | |||||
| } | |||||
| // UnmarshalSession wil unmarshal a JSON string into a session. | |||||
| func (p *Provider) UnmarshalSession(data string) (goth.Session, error) { | |||||
| s := &Session{} | |||||
| err := json.NewDecoder(strings.NewReader(data)).Decode(s) | |||||
| return s, err | |||||
| } |
+ 1
- 0
vendor/modules.txt
View File
| github.com/markbates/goth/providers/github | github.com/markbates/goth/providers/github | ||||
| github.com/markbates/goth/providers/gitlab | github.com/markbates/goth/providers/gitlab | ||||
| github.com/markbates/goth/providers/google | github.com/markbates/goth/providers/google | ||||
| github.com/markbates/goth/providers/nextcloud | |||||
| github.com/markbates/goth/providers/openidConnect | github.com/markbates/goth/providers/openidConnect | ||||
| github.com/markbates/goth/providers/twitter | github.com/markbates/goth/providers/twitter | ||||
| # github.com/mattn/go-isatty v0.0.7 | # github.com/mattn/go-isatty v0.0.7 |
+ 2
- 0
web_src/js/index.js
View File
| case 'github': | case 'github': | ||||
| case 'gitlab': | case 'gitlab': | ||||
| case 'gitea': | case 'gitea': | ||||
| case 'nextcloud': | |||||
| $('.oauth2_use_custom_url').show(); | $('.oauth2_use_custom_url').show(); | ||||
| break; | break; | ||||
| case 'openidConnect': | case 'openidConnect': | ||||
| $('.oauth2_token_url input, .oauth2_auth_url input, .oauth2_profile_url input, .oauth2_email_url input').attr('required', 'required'); | $('.oauth2_token_url input, .oauth2_auth_url input, .oauth2_profile_url input, .oauth2_email_url input').attr('required', 'required'); | ||||
| $('.oauth2_token_url, .oauth2_auth_url, .oauth2_profile_url, .oauth2_email_url').show(); | $('.oauth2_token_url, .oauth2_auth_url, .oauth2_profile_url, .oauth2_email_url').show(); | ||||
| break; | break; | ||||
| case 'nextcloud': | |||||
| case 'gitea': | case 'gitea': | ||||
| case 'gitlab': | case 'gitlab': | ||||
| $('.oauth2_token_url input, .oauth2_auth_url input, .oauth2_profile_url input').attr('required', 'required'); | $('.oauth2_token_url input, .oauth2_auth_url input, .oauth2_profile_url input').attr('required', 'required'); |
Loading…
